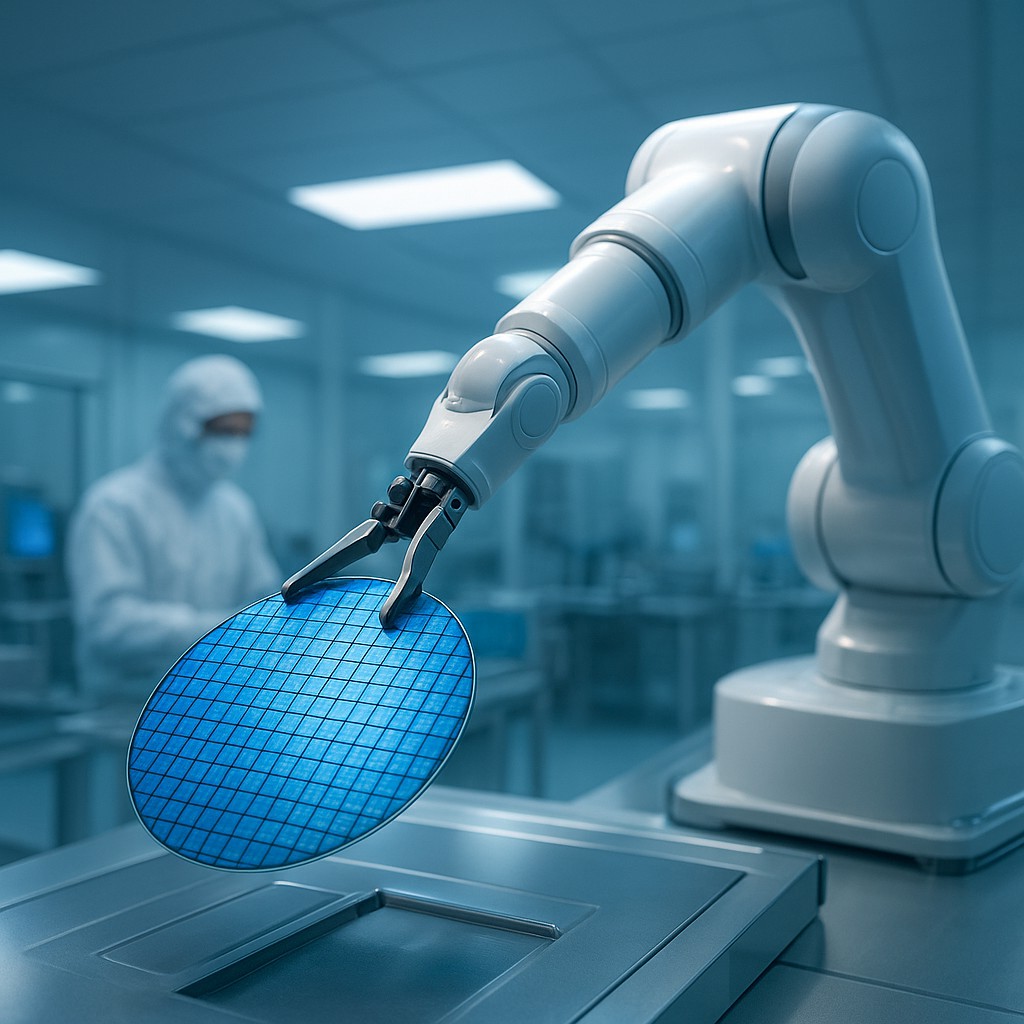
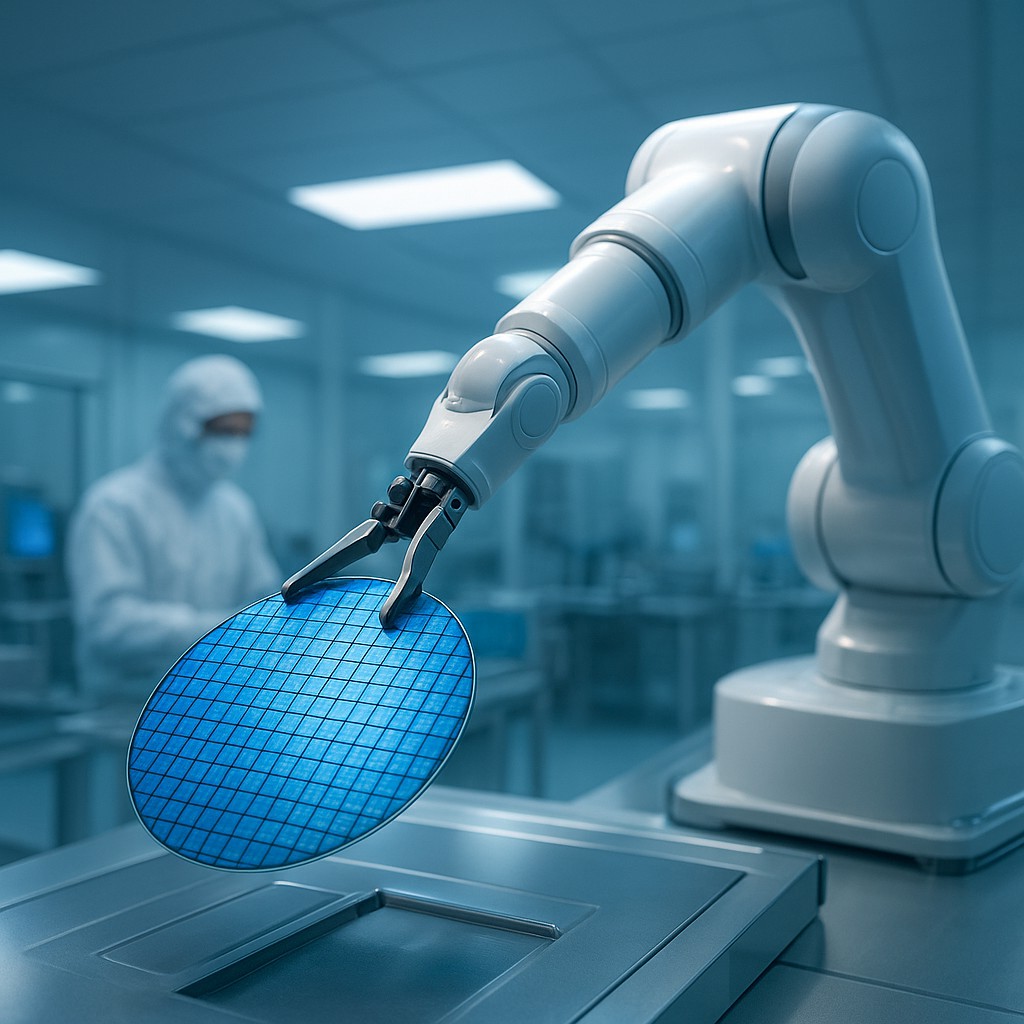
In the quiet, climate-controlled corners of a high-tech cleanroom, a robotic arm maneuvers a silicon wafer with more precision than a neurosurgeon. For decades, the global trade of these tiny, incredible objects followed a simple logic: if a company wanted to buy a chip and had the money, the transaction went through. We treated microchips like commodities - no different from wheat or oil - where a border agent's only concerns were taxes and quantity. However, the world has changed. Our silicon friends have evolved from mere "computer parts" into the literal brainpower behind national security, artificial intelligence, and global surveillance.
Because these chips are now so powerful, the old way of monitoring trade is no longer enough. It isn't enough to know what an item is; governments now desperately need to know what that item is going to do once it reaches its destination. This shift has moved us away from traditional "list-based" controls, where officials simply checked off items on a forbidden list, toward a much more complex system known as "end-use" controls. This new philosophy turns every chip manufacturer into a private investigator, forcing them to look past the sale and into the true intentions of their customers.
From Physical Goods to Intended Actions
To understand why this change matters, we have to look at the limits of old-school trade. In the past, if a country wanted to stop a neighbor from building a tank, they would simply ban the export of heavy armor plating or specialized engines. This worked because a tank engine is very difficult to disguise as a lawnmower engine. In the world of semiconductors, however, the lines are frustratingly blurry. A high-end Graphics Processing Unit (GPU) can be used to render the fluffy fur of a cat in a video game, but 그 same exact chip can also calculate the flight path of a hypersonic missile or power a massive surveillance network that tracks millions of people.
The hardware is identical, but the intent is worlds apart. This "dual-use" nature of technology is what makes modern trade policy so difficult to navigate. End-use controls are the government's answer to this dilemma. Instead of banning the chip itself, the law focuses on the "end-user" and the "end-use." If your company is using chips to build a better medical diagnostic tool, you get a green light. If those same chips are destined for a laboratory working on autonomous weapons, the light turns red. This shift means that the "use case" has become a regulated part of the product, just as much as the internal wiring.
Monitoring the Destiny of a Microchip
When a government implements end-use controls, they are essentially asking the exporter to perform a background check on the entire history and future of their product. This is no simple task. It requires the kind of deep-dive "Know Your Customer" (KYC) protocols previously reserved for the banking industry. Companies like Nvidia, TSMC, and Intel must now maintain sophisticated compliance departments to scrutinize who is buying their hardware and, more importantly, what those buyers plan to do with it. This involves checking the "Entity List," a roster of companies and organizations deemed to be security risks.
The complexity increases because these controls often follow the product regardless of where it was made. Under rules like the Foreign Direct Product Rule, if a piece of equipment was designed with American software or built using American tools, the United States can claim jurisdiction over where that product ends up, even if the final sale happens between two other countries. This creates a regulatory web that wraps around the entire globe. It turns the supply chain into a digital ledger where every handoff must be documented and every promise of "peaceful use" must be verified.
Throttling Progress as a Strategy
Why go through all this trouble instead of just banning everything? The goal of modern end-use controls is "targeted de-risking." Governments want to allow their domestic companies to keep making money in the global market, but they want to "throttle" the technological progress of potential rivals. By blocking specific high-end computing uses, a country can let its competitors have the chips needed for basic electronics while withholding the "frontier" hardware required for the next generation of warfare or economic dominance.
| Control Type |
Focus Area |
Primary Mechanism |
Challenge |
| List-Based |
The Item |
Technical specs and metrics |
Quickly becomes outdated as tech evolves |
| End-User |
The Person/Entity |
Blocklists and entity screenings |
Entities change names or use front companies |
| End-Use |
The Activity |
Verifying the specific project |
Extremely hard to monitor after the sale |
| Destination |
The Geography |
Embargoes on specific countries |
Items can be smuggled across borders |
This "high fence, small yard" approach aims to protect a narrow set of critical technologies with very high barriers to entry. For example, recent restrictions have specifically targeted chips used for "Advanced Computing" and "Supercomputing." The idea is that while a country might be able to buy thousands of lower-tier chips for smartphones, they will be blocked from acquiring the powerhouse processors needed to train a massive Artificial Intelligence model. It is a game of strategic bottlenecks, where the goal is to stay two or three steps ahead in the global tech race.
The Ghost of the Secondary Market
Despite the best efforts of regulators, end-use controls face a massive, shadowy obstacle: the secondary market. Once a chip is sold to a legitimate distributor in a "safe" country, it enters a vast ocean of global commerce. It can be resold, refurbished, or "diverted" through multiple shell companies before ending up in a restricted laboratory in a sanctioned nation. These "gray market" transactions are nearly impossible to track because chips are small, high-value, and easy to hide in a suitcase or a generic shipping crate.
Governments are currently experimenting with high-tech solutions to this problem. Some are proposing digital "tags" or hardware-level "kill switches" that could theoretically disable a chip if it is moved to an unauthorized location. Others are pushing for more transparency among distributors, requiring third-party resellers to adopt the same strict vetting processes as the original manufacturers. However, as long as there is a high demand for restricted silicon, someone will try to find a loophole, making the enforcement of end-use controls a permanent game of cat and mouse.
Corporate Responsibility in a Geopolitical World
For the engineers and CEOs of the world, these rules have fundamentally changed the nature of business. It is no longer enough to be a brilliant innovator; you must also be a savvy geopolitical actor. A company that fails to properly vet its customers can face massive fines, the loss of export licenses, or even criminal charges. This has led to a "de-risking" trend where companies simplify their supply chains or build "clean" factories that stay away from restricted components just to avoid the headache of compliance.
This pressure trickles down to the research level. When designing a new chip, engineers must now consider if its performance will trigger a "trade threshold." If they make a chip too fast or too efficient, it might become subject to end-use controls that limit where it can be sold. We are entering an era where the laws of physics are competing with the laws of international trade, and the winners will be those who can innovate within the constraints of a highly regulated world.
Navigating the Future of Digital Borders
As we look toward the future, the concept of a sovereign border is moving away from the physical ground and into the architecture of our devices. The "End-Use" philosophy suggests that a piece of hardware is never truly "owned" by the buyer; instead, it is "leased" under a set of conditions that the country of origin can revoke. This creates a paradox of ownership that will likely define the digital economy for decades. We are seeing the rise of "technological sovereignty," where the flow of information and the power of computation are the most guarded assets on the planet.
Understanding this shift lets you see the world not just as a collection of products, but as a network of intents and permissions. The next time you see a headline about a trade war or a chip shortage, remember that it is about more than money. It is a quiet, high-stakes struggle to define who gets to build the future and what that future is allowed to look like. By mastering the nuances of end-use controls, you are gaining a window into the machinery of global power, where a single silicon chip can carry the weight of an entire nation's security.